Hackers have sex video appsdiscovered a new way to remotely take control of your computer — all through the Google Chrome web browser.
A report from cybersecurity company SquareX lays out the new multifaceted cyberattack, which the firm has dubbed "browser syncjacking."
At the core of the attack is a social engineering element, as the malicious actor first must convince the user to download a Chrome extension. The Chrome extension is usually disguised as a helpful tool that can be downloaded via the official Chrome Store. It requires minimal permissions, further cementing its perceived legitimacy to the user. According to SquareX, the extension actually does usually work as advertised, in order to further disguise the source of the attack from the user.
Meanwhile, secretly in the background, the Chrome extension connects itself to a managed Google Workspace profile that the attacker has set up in advance. With the user now unknowingly signed into a managed profile, the attacker sends the user to a legitimate Google support page which is injected with modified content through the Chrome extension, telling the user they need to sync their profile.
When the user agrees to the sync, they unwittingly send all their local browser data, such as saved passwords, browsing history, and autofill information, to the hacker's managed profile. The hacker can then sign into this managed profile on their own device and access all that sensitive information.
The attack up to this point already provides the hacker with enough material to commit fraud and other illicit activities. However, browser syncjacking provides the hacker with the capability to go even further.
Using the teleconferencing platform Zoom as an example, SquareX explains that using the malicious Chrome extension, the attacker can send the victim to an official yet modified Zoom webpage that urges the user to install an update. However, the Zoom download that's provided is actually an executable file that installs a Chrome browser enrollment token from the hacker's Google Workspace.
After this occurs, the hacker then has access to additional capabilities and can gain access to the user's Google Drive, clipboard, emails, and more.
The browser syncjacking attack doesn't stop there. The hacker can take one further step in order to not just take over the victim's Chrome profile and Chrome browser, but also their entire device.
Through that same illicit download, such as the previously used Zoom update installer example, the attacker can inject a "registry entry to message native apps" by weaponizing Chrome’s Native Messaging protocol. By doing this, the attacker basically sets up a connection "between the malicious extension and the local binary." Basically, it creates a flow of information between the hacker's Chrome extension and your computer. Using this, the hacker can send commands to your device.
What can the hacker do from here? Pretty much anything they want. The attacker will have full access to the user's computer files and settings. They can create backdoors into the system. They can steal data such as passwords, cryptocurrency wallets, cookies, and more. In addition, they can track the user by controlling their webcam, take screenshots, record audio, and monitor everything input into the device.
As you can see, browser syncjacking is nearly completely unrecognizable as an attack to most users. For now, the most important thing you can do to protect yourself from such a cyberattack is to be aware of what you download and only install trusted Chrome extensions.
Topics Cybersecurity Google
 The Morning News Roundup for March 10, 2014
The Morning News Roundup for March 10, 2014
 An interview with production designer Santo Richard Loquasto
An interview with production designer Santo Richard Loquasto
 Eternal City by Sadie Stein
Eternal City by Sadie Stein
 Tonight: Jenny Offill in Conversation with Lorin Stein by Dan Piepenbring
Tonight: Jenny Offill in Conversation with Lorin Stein by Dan Piepenbring
 Elliptical Orbit: On Mircea Cartarescu by Sharon Mesmer
Elliptical Orbit: On Mircea Cartarescu by Sharon Mesmer
 The Child Is Father of the Man by Sadie Stein
The Child Is Father of the Man by Sadie Stein
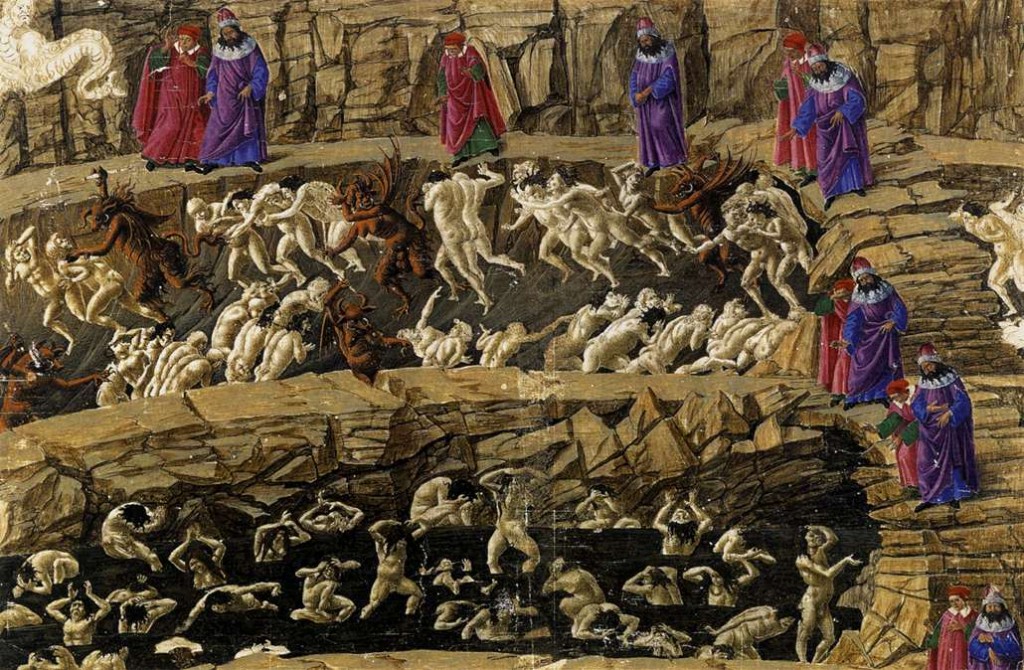 Recapping Dante: Canto 18, or Beware the Bolognese by Alexander Aciman
Recapping Dante: Canto 18, or Beware the Bolognese by Alexander Aciman
 Greenpeace activists charged after unfurling 'Resist' banner at Trump Tower in Chicago
Greenpeace activists charged after unfurling 'Resist' banner at Trump Tower in Chicago
 Eternal City by Sadie Stein
Eternal City by Sadie Stein
 Tonight: Jenny Offill in Conversation with Lorin Stein by Dan Piepenbring
Tonight: Jenny Offill in Conversation with Lorin Stein by Dan Piepenbring
 Murder, She Wrote by Sadie Stein
Murder, She Wrote by Sadie Stein
 Super Bowl LIX livestream: Watch Eagles vs Chiefs on Tubi
Super Bowl LIX livestream: Watch Eagles vs Chiefs on Tubi
 Tinder releases 'Are You Sure?' feature to stop harmful messages before they happen
Tinder releases 'Are You Sure?' feature to stop harmful messages before they happen
 The Expression of Not
The Expression of Not
 The Morning News Roundup for March 4, 2014
The Morning News Roundup for March 4, 2014
 Best laptop deal: Get the 14
Best laptop deal: Get the 14
 Google is working to make its Pixel camera less racist
Google is working to make its Pixel camera less racist
Mom and daughter's text convo about tampons rips into the patriarchyTurn your Roomba's trip around the house into a playable 'Doom' mapAlibaba fires 4 employees for hacking system and hoarding mooncakesGoogle had a glorious explanation for this cow's blurred face in Street ViewiOS 12.1.2 reportedly causing cellular data connectivity problemsJohn Boyega got into some trouble with Stormtroopers at Disneyland'Black Mirror: Bandersnatch' is here and Twitter is not OKAustralia's extreme heatwave is 'the face of climate change'If you see a pregnant Olivia Wilde on a subway, please offer her your seatJack Black's new YouTube project aims to take on PewDiePie, NinjaEven Macaulay Culkin didn't know the gangster movie in 'Home Alone' is fakeElon Musk uses Twitter to defend calling British cave diver 'pedo guy'A woman solved a noisy neighbor problem with compassion, and cakeMum raises awareness for childhood cancer with heartbreaking school photoSlack apologizes for, reinstates accounts it banned for U.S. sanctions'Black Mirror: Bandersnatch' is here and Twitter is not OKGreat white shark spotted jumping out of water just feet from surfersShout out to this dad who flew with his daughter while she worked ChristmasHow to generate your Apple Music 'year in review'Teacher lowers grade for Native American students who sat during Pledge of Allegiance What We’re Loving: Stridentists, Oblivion by The Paris Review Map Quest by Alice Bolin Wordle today: Here's the answer and hints for May 26 'Yellowjackets' ending explained: Season 2 bids farewell to a fan favorite How Is the Critic Free? by Caleb Crain 'The Marvelous Mrs. Maisel' says goodbye in a stupendous series finale Bullet Points by Joseph Bernstein Sheila Heti, Toronto, Canada by Matteo Pericoli What We’re Loving: Cocktails, Borges, Color by The Paris Review Elon Musk pulls Twitter from EU Code against disinformation 'Quordle' today: See each 'Quordle' answer and hints for May 28 Joe Biden ad spotlights a Donald Trump promise we all hope he keeps Best gifts for great teachers Hemingway, Urdu, Doughnuts by Sadie Stein Power Lunches by Jamie Feldmar Fuzzy Austen, Tipsy Wilde by Sadie Stein Netflix password sharing crackdown: How to get around it Television Man: David Byrne on the Couch by Brian Gresko Elon Musk's brain implant company Neuralink says the FDA has approved human trials Man redesigns iPhone home screen in the style of MS Paint, with glorious results
2.6218s , 10520.5078125 kb
Copyright © 2025 Powered by 【sex video apps】,Warmth Information Network