Hackers have Weaknesses Of Female Employees Who Are Promoted Quickly (2025)discovered a new way to remotely take control of your computer — all through the Google Chrome web browser.
A report from cybersecurity company SquareX lays out the new multifaceted cyberattack, which the firm has dubbed "browser syncjacking."
At the core of the attack is a social engineering element, as the malicious actor first must convince the user to download a Chrome extension. The Chrome extension is usually disguised as a helpful tool that can be downloaded via the official Chrome Store. It requires minimal permissions, further cementing its perceived legitimacy to the user. According to SquareX, the extension actually does usually work as advertised, in order to further disguise the source of the attack from the user.
Meanwhile, secretly in the background, the Chrome extension connects itself to a managed Google Workspace profile that the attacker has set up in advance. With the user now unknowingly signed into a managed profile, the attacker sends the user to a legitimate Google support page which is injected with modified content through the Chrome extension, telling the user they need to sync their profile.
When the user agrees to the sync, they unwittingly send all their local browser data, such as saved passwords, browsing history, and autofill information, to the hacker's managed profile. The hacker can then sign into this managed profile on their own device and access all that sensitive information.
The attack up to this point already provides the hacker with enough material to commit fraud and other illicit activities. However, browser syncjacking provides the hacker with the capability to go even further.
Using the teleconferencing platform Zoom as an example, SquareX explains that using the malicious Chrome extension, the attacker can send the victim to an official yet modified Zoom webpage that urges the user to install an update. However, the Zoom download that's provided is actually an executable file that installs a Chrome browser enrollment token from the hacker's Google Workspace.
After this occurs, the hacker then has access to additional capabilities and can gain access to the user's Google Drive, clipboard, emails, and more.
The browser syncjacking attack doesn't stop there. The hacker can take one further step in order to not just take over the victim's Chrome profile and Chrome browser, but also their entire device.
Through that same illicit download, such as the previously used Zoom update installer example, the attacker can inject a "registry entry to message native apps" by weaponizing Chrome’s Native Messaging protocol. By doing this, the attacker basically sets up a connection "between the malicious extension and the local binary." Basically, it creates a flow of information between the hacker's Chrome extension and your computer. Using this, the hacker can send commands to your device.
What can the hacker do from here? Pretty much anything they want. The attacker will have full access to the user's computer files and settings. They can create backdoors into the system. They can steal data such as passwords, cryptocurrency wallets, cookies, and more. In addition, they can track the user by controlling their webcam, take screenshots, record audio, and monitor everything input into the device.
As you can see, browser syncjacking is nearly completely unrecognizable as an attack to most users. For now, the most important thing you can do to protect yourself from such a cyberattack is to be aware of what you download and only install trusted Chrome extensions.
Topics Cybersecurity Google
 Mountains Hidden by Clouds: A Conversation with Anuradha Roy by Pankaj Mishra
Mountains Hidden by Clouds: A Conversation with Anuradha Roy by Pankaj Mishra
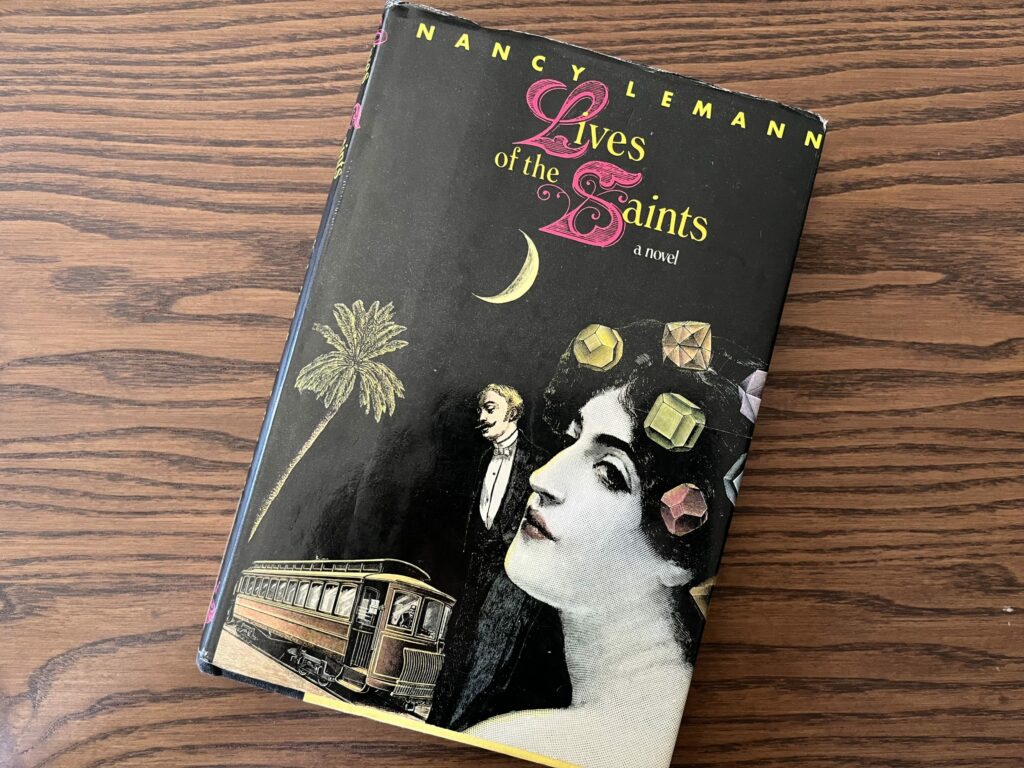 The Entangled Life: On Nancy Lemann by Krithika Varagur
The Entangled Life: On Nancy Lemann by Krithika Varagur
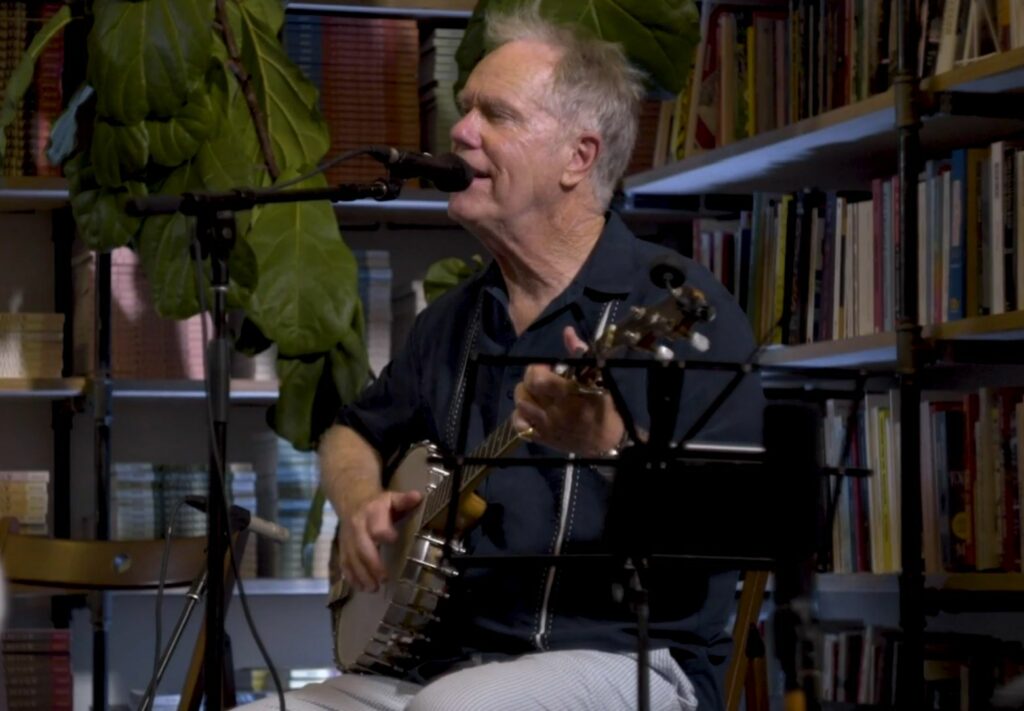 Watch Loudon Wainwright III Perform Live at the Paris Review Offices by The Paris Review
Watch Loudon Wainwright III Perform Live at the Paris Review Offices by The Paris Review
 Precursors to Today's Technology: These Products Had the Right Vision
Precursors to Today's Technology: These Products Had the Right Vision
 September Notebook, 2018 by Daniel Poppick
September Notebook, 2018 by Daniel Poppick
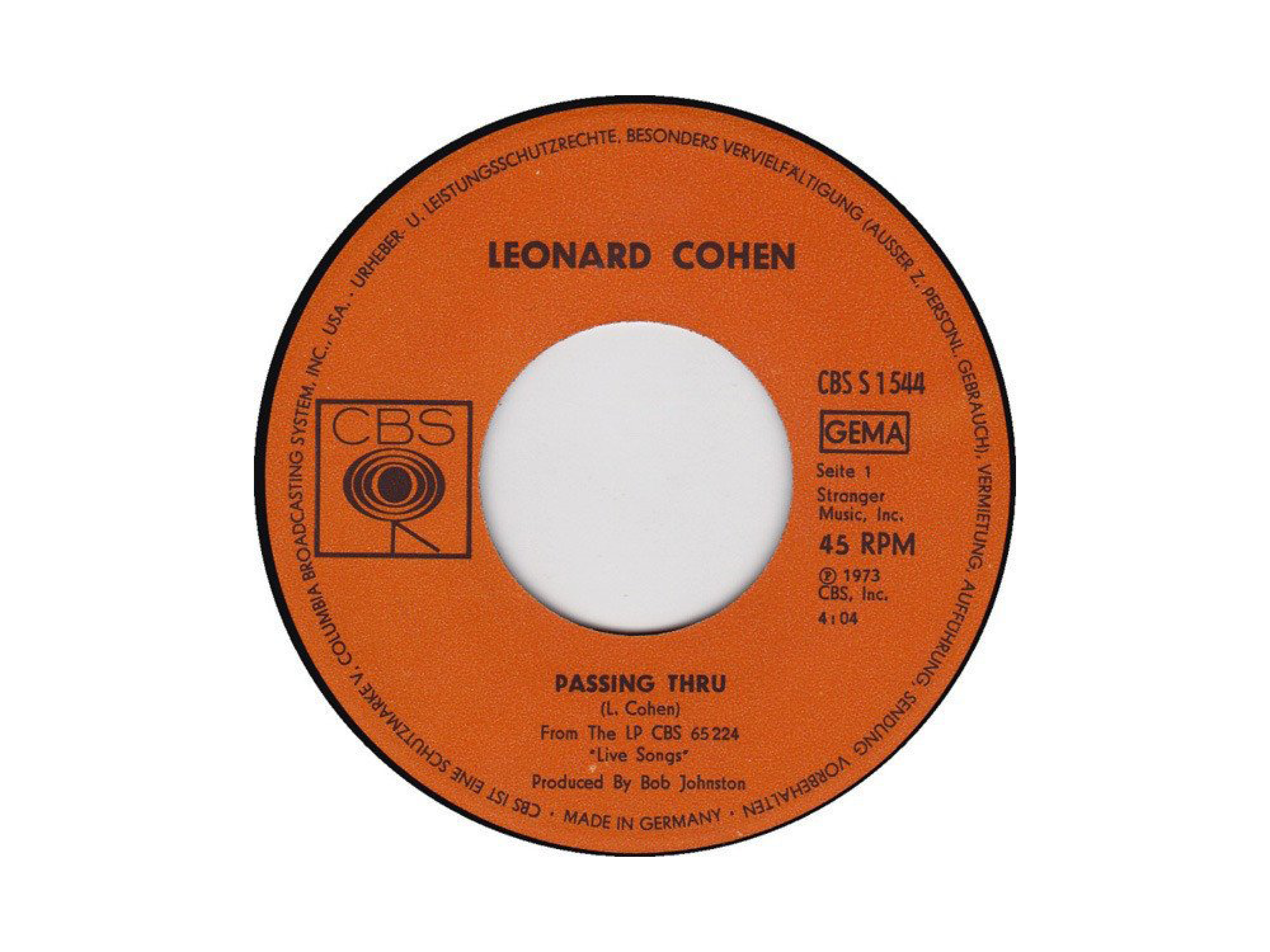 Passing Through: On Leonard Cohen by Andrew Martin
Passing Through: On Leonard Cohen by Andrew Martin
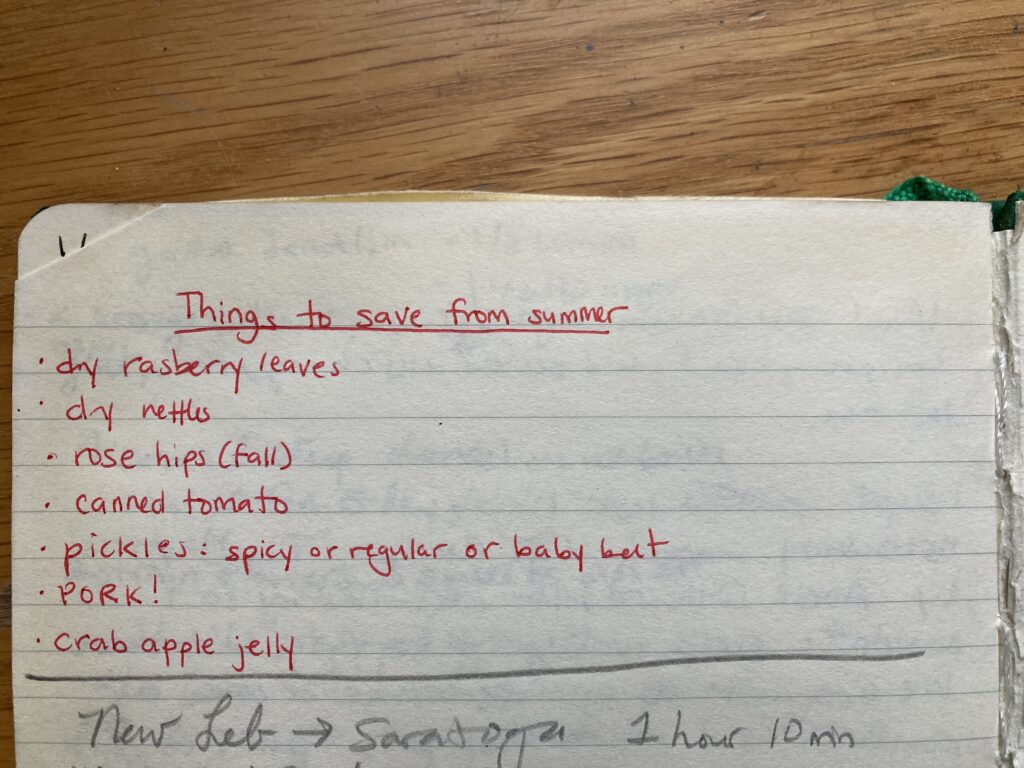 Solstice Diaries by Ellyn Gaydos
Solstice Diaries by Ellyn Gaydos
 Golden State Warriors vs. Los Angeles Lakers 2025 livestream: Watch NBA online
Golden State Warriors vs. Los Angeles Lakers 2025 livestream: Watch NBA online
 Apple Vision Pro scalpers are making a killing. Here's why.
Apple Vision Pro scalpers are making a killing. Here's why.
 Here's how I feel about all this Stephen Hawking 'news' going around
Here's how I feel about all this Stephen Hawking 'news' going around
 Best espresso deal: Get a free $120 Amazon credit with the Ninja Luxe Café Premier
Best espresso deal: Get a free $120 Amazon credit with the Ninja Luxe Café Premier
 Magical scientists name spider after the Sorting Hat from Harry Potter
Magical scientists name spider after the Sorting Hat from Harry Potter
 On Cary Grant, Darryl Pinckney, and Whit Stillman by The Paris Review
On Cary Grant, Darryl Pinckney, and Whit Stillman by The Paris Review
 Wordle today: The answer and hints for January 25
Wordle today: The answer and hints for January 25
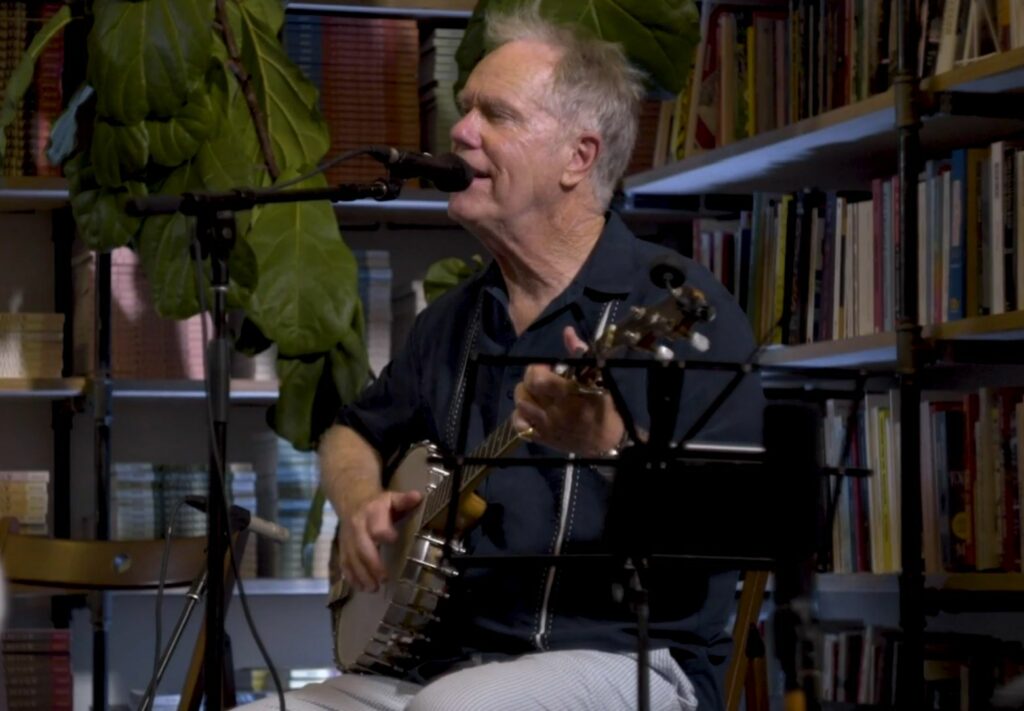 Watch Loudon Wainwright III Perform Live at the Paris Review Offices by The Paris Review
Watch Loudon Wainwright III Perform Live at the Paris Review Offices by The Paris Review
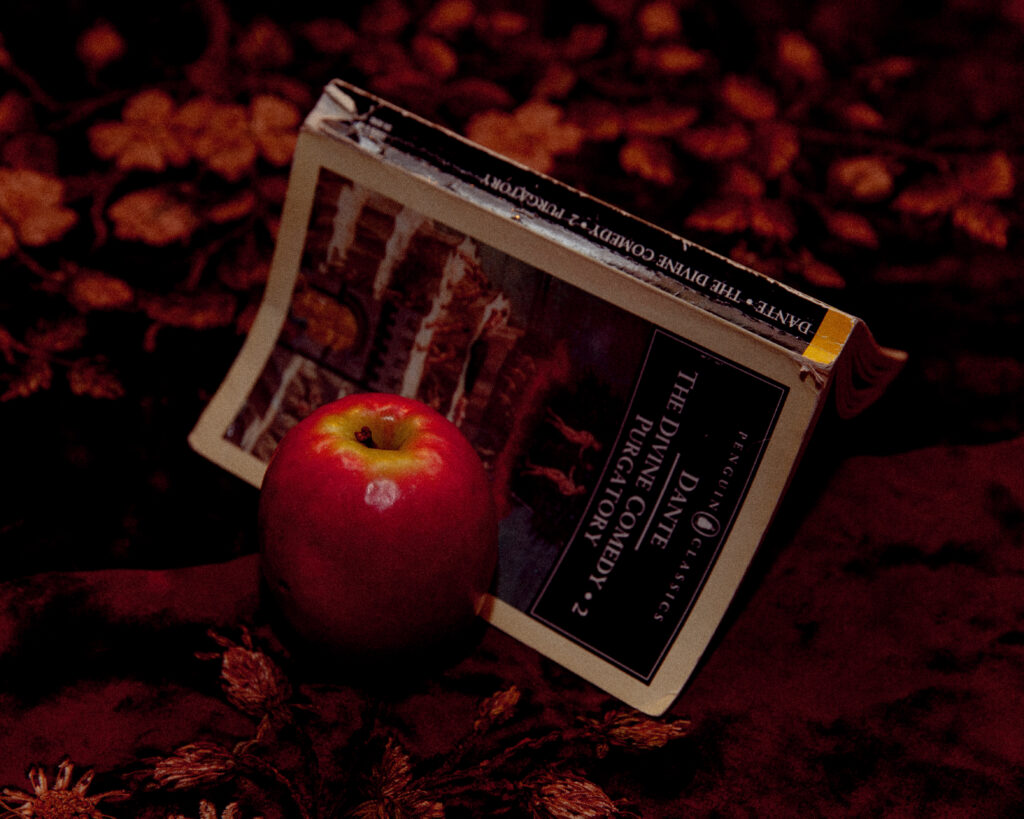 Cooking with Dante Alighieri by Valerie Stivers
Cooking with Dante Alighieri by Valerie Stivers
 In Paris Agreement speech, Trump never acknowledged the reality of global warming
In Paris Agreement speech, Trump never acknowledged the reality of global warming
 Donald Trump's anti
Donald Trump's anti
A Pimp with a Heart of Gold by Liam SherwinAnnouncing Our Winter Issue by Emily StokesDirty Brown Subaru Outback by Kelan NeeMy Strawberry Plants: On Marcottage by Kate BriggsSally Jackson is the notDare to Leave a Trace: On A City of Sadness by Michelle Kuo’88 Toyota Celica by Sam AxelrodAn Illegible Quartet and Choreographic Research by The Paris ReviewTech and cash is not enough when it comes to health and climate changeHow to edit photosTwo Strip Clubs, Paris and New Hampshire by Lisa CarverNetflix teases giant 2024 movie and TV lineup: Watch the trailerOn Sven Holm’s Novella of Nuclear Disaster by Jeff VanderMeerCorrection by The Paris ReviewHow to have car sexHow to have car sexCitroën Cactus by Holly ConnollyThe Sphere by Elena Saavedra BuckleyGoogle releases sneak peek of its Super Bowl commercialChild Reading by Timmy Straw Instagram and Facebook users report messaging issues The best video games of 2020 How classic video game remakes took the edge off 2020 Humanity dumped 37 billion tons of CO2 into the atmosphere in 2020 Young activists share tips for staying politically involved YouTube will finally remove videos that spread misinformation about the 2020 election Star Wars movie 'Rogue Squadron' coming from director Patty Jenkins Apple's secret workout lab could lead to a super powerful Apple Watch A third royal baby's on the way to rival George and Charlotte's cuteness Burning Man 2017 is as wild and amazingly artistic as you expected Taylor Swift’s ‘evermore’ review: A thoughtful note for a dark year Tyler Perry is giving $1 million to Harvey relief—but there's a controversial catch Google adds authoritative info on COVID Apple's $549 AirPods Max are already sold out for this year How this 16th century love triangle anticipated the 'Disloyal Man' meme GoFundMe, now 10, had a historic year of charitable giving Watch Justin Trudeau's awkward pause before he calls Donald Trump 'authentic' Vanessa Carlton offers to replace damaged piano after seeing man's heartbreaking video Cyclist dabs for Google Maps camera, instantly becomes an internet hero The best meteor shower of 2020 is about to light up our atmosphere
2.079s , 10137.53125 kb
Copyright © 2025 Powered by 【Weaknesses Of Female Employees Who Are Promoted Quickly (2025)】,Warmth Information Network